Hey, tech warriors and cybersecurity explorers!
Ever stared at a URL and thought, “Wait a second, something feels off here… but I can’t quite put my finger on it”? Or maybe you clicked a link that looked exactly like your bank’s domain name, only to find yourself staring at a shady login page. If that sounds familiar (or frightening), then welcome to the sneaky world of homoglyph attacks — one of the most elegant deceptions in a cybercriminal’s toolkit.
In this article, we’re going to crack open the what, how, and why of homoglyph attacks in a way that’s not just digestible, but also enjoyable (because we techies like our coffee strong and our explanations stronger). So, grab a cup and let’s dive in.
What is a Homoglyph Attack?
In the simplest terms, a homoglyph attack is a visual deception technique where an attacker uses characters that look similar (or identical) to legit ones to spoof domains, usernames, file names, or even command-line arguments.
Let me give you a quick visual:
| Legit | Spoofed |
| google.com | gооgle.com (using Cyrillic ‘o’s) |
| paypal.com | paypaL.com (capital L instead of lowercase ‘l’) |
| amazon.com | аmazon.com (Cyrillic ‘a’) |
You see, these attacks aren’t about brute force or clever malware. They prey on human vision and our brain’s tendency to autocorrect familiar patterns. Your eyes read “google.com” but your system is pointing to an attacker-controlled site.
This type of cyberattack is a subset of typosquatting and IDN spoofing (Internationalized Domain Names), and it’s frighteningly effective.
How Do Homoglyph Attacks Work?
Homoglyph attacks exploit the Unicode standard. While English uses the basic ASCII set, Unicode supports hundreds of thousands of characters, including letters from Cyrillic, Greek, Arabic, Devanagari, and others that look nearly identical to Latin characters.
Let’s break it down like a pro:
- Registration of Fake Domains:
Attackers register domains using visually similar characters (like Cyrillic ‘а’ or Greek ‘ο’) that mimic trusted brands. - Spoofed Websites or Emails:
These domains are then used in phishing campaigns, malicious redirects, or even fake login portals. - Social Engineering:
The attacker tricks users into clicking these URLs by embedding them in emails, SMS, ads, or even chat messages. - Harvesting Credentials or Spreading Malware:
Once on the spoofed site, users may unknowingly enter their credentials, download infected files, or trigger scripts.
Real-World Examples of Homoglyph Attacks
Let’s talk reality. These attacks aren’t just theory — they’re happening right now:
- 2017 – Xudong Zheng’s Proof of Concept:
A security researcher registered https://www.xn--80ak6aa92e.com, which displays as “apple.com” in browsers supporting IDNs. No warnings, no suspicion — just pure deception. - Paypal & Google Spoofs:
Attackers have repeatedly created domains like paypaI.com (capital ‘i’), goog1e.com (number 1 instead of L), and even support.goggle.com to phish users. - GitHub Repositories Hijack:
A more technical version involves creating repo names or usernames using homoglyphs to impersonate real developers, especially in supply-chain attacks. - Recent Attacks (2023-2024):
- Domains mimicking financial institutions and cryptocurrency platforms were registered using homoglyph techniques.
- A phishing campaign impersonated Microsoft 365 login portals using lookalike domains targeting business email compromise (BEC).
Scary, right? Because it looks so real.
Who is Targeted?
Everyone. But some groups are more vulnerable than others:
- Corporate Users & Executives: Often targeted in spear-phishing attacks.
- Developers & DevOps: Through spoofed package names (e.g., NPM, PyPI, GitHub).
- General Public: Via social media messages, fake login pages, or typo-ridden URLs.
- Financial & Crypto Users: Where stakes are high and attackers are relentless.
If you own a domain, run a business, or even just browse regularly — you’re a target.
Why Are Homoglyph Attacks So Dangerous?
Let’s get something straight — this isn’t about lazy users being phished. It’s about:
- Perfect Visual Deception: Even trained eyes can miss these characters.
- Bypassing Filters: Many filters focus on known domains or ASCII-based tricks.
- Open Unicode Playground: The sheer number of visually similar characters in Unicode gives attackers endless possibilities.
- Trust Exploitation: If someone trusts the domain in a message, they’re more likely to engage.
This makes homoglyph attacks low-effort, low-cost, and high-impact.
Technical Detection & Prevention Strategies
Alright, enough of the doom and gloom. Let’s talk about how we fight back.
1. Browser & OS-Level Protections
- Modern browsers like Chrome, Firefox, and Safari have IDN detection logic. They show the Punycode version of the URL if mixed scripts are detected.
- Example:
- https://xn--pple-43d.com → Displays as apple.com or in Punycode, depending on locale settings.
- Example:
- Limitations: This behavior isn’t always consistent and varies by browser and user locale.
2. Email Gateway Filters
- Email security tools (like Proofpoint, Mimecast, Microsoft Defender) can be configured to flag or rewrite domains with Unicode anomalies.
- Training content filters to look for suspicious lookalikes using homograph detection libraries.
3. Fuzzy Matching Algorithms
- Tools like DNSTwist, Homoglyph.py, or URLCrazy can scan for lookalike domains.
- These tools generate permutations of your brand name or domain and check for registered variants.
4. Domain Registration Monitoring
- Monitor new domain registrations that are visually similar to your brand.
- Services like DomainTools, BrandShield, or DNSTwist can automate alerts.
5. Zero Trust & MFA Everywhere
- If your credentials do get phished, MFA (multi-factor authentication) can block unauthorized access.
- Combine this with a Zero Trust network model to verify identity before granting access.
6. User Awareness & Training
- Teach users how to hover before clicking.
- Educate about the risks of lookalike domains.
- Use simulated phishing exercises to reinforce detection skills.
Proactive Defense Tips for Enterprises
- Whitelist Known Domains: Lock down outbound traffic to known, verified domains.
- HSTS & HTTPS: Enforce strict HTTPS and HTTP Strict Transport Security to avoid redirection traps.
- Use Custom Error Pages: Prevent your own domain from being abused in typo-based attacks.
- Register Lookalike Domains: Buy up the most common typo/homoglyph variations of your domain.
Wrap-Up: It’s Not Just About Seeing, It’s About Noticing
Homoglyph attacks are like the perfect illusion — hiding in plain sight. The biggest danger? They work because they don’t raise suspicion.
In today’s digital landscape, where visual trust matters and attackers know it, we must go beyond what the eye can see. From tech defenses to human awareness, battling homoglyph attacks is a team sport.
So next time you get a link that “looks fine”… pause. Hover. Inspect. Question. Because in cybersecurity, being paranoid isn’t a bug — it’s a feature.
Stay sharp, stay safe, and may your URLs always be true.
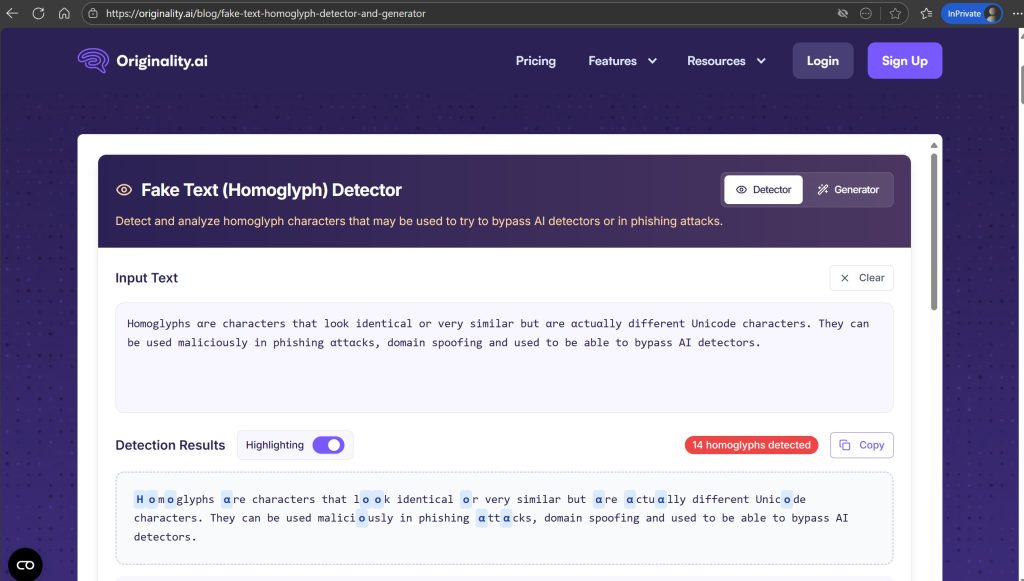
You can detect Homoglyph text on below URL
https://originality.ai/blog/fake-text-homoglyph-detector-and-generator